What hotels need on data security and compliance in 2026: GDPR posture, EU residency, vendor due diligence, audit logs, and the contract terms that actually matter.
â€
Disclaimer: The insights and discussions presented in this blog series are intended to provide a broad overview of modern hotel technology stacks. The content is designed for informational purposes and may not reflect the most recent market developments. Every hotel's needs and circumstances are unique; thus, the technology solutions and strategies discussed should be tailored to meet specific operational requirements. Readers are advised to conduct further research or consult with industry experts before making any significant technological investments or strategic decisions.
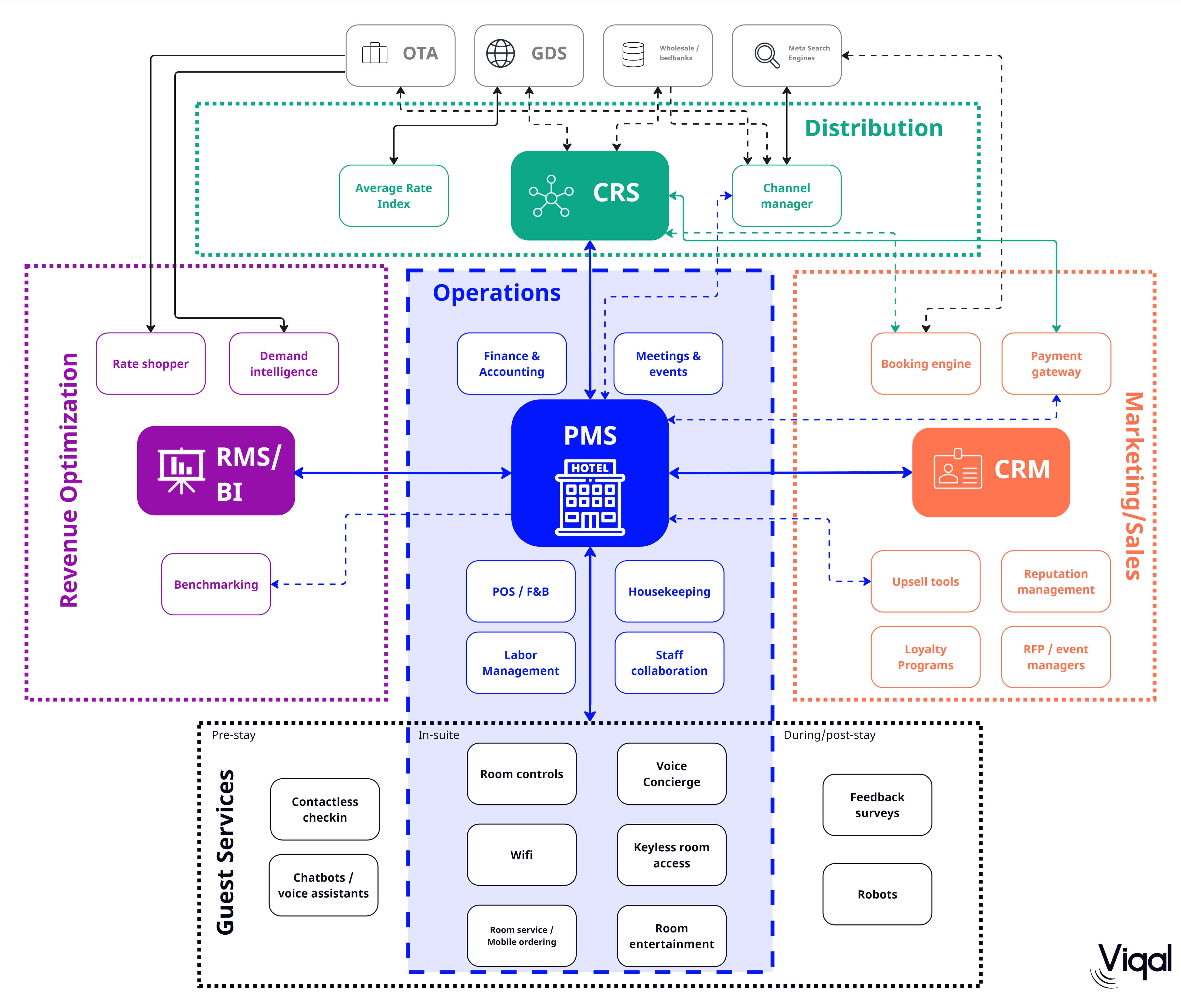
Hotels collect a lot of sensitive data: passport scans, card details, dietary needs, occasionally medical notes when a guest asks for a hypoallergenic room. Protecting it is partly about regulation and partly about not waking up to a story in The Times. Breaches in hospitality have a particular flavour because the data is rich (identity plus payment plus location) and the perimeter is wide: a chatbot vendor, a Wi-Fi provider, a marketing tool. The discipline below is what serious operators put in place. The team running a digital concierge conversation, or any AI tool talking to guests, sits squarely inside that perimeter and needs the same scrutiny as the PMS.
â€
For European operators, GDPR is the regulation that matters most. It rests on a few principles worth re-reading every year: a defined lawful basis for processing (Article 6), data minimisation (Article 5), the right of access and erasure (Articles 15 and 17), and breach notification within 72 hours (Article 33). The fines are not theoretical. Marriott was fined GBP 18.4 million by the ICO in 2020 over the Starwood breach. H&M took a EUR 35 million GDPR fine in the same period. Smaller properties are not exempt. The local DPA in your country can and does act on complaints from individual guests. One pattern we see often: a hotel keeps reservation history forever 'in case the guest comes back', without a documented retention policy. That is the easy GDPR violation. Below are the regulations to know:
â€
Breaches in our industry rarely come from sophisticated nation-state actors. They come from a phished front-desk password, an unpatched server in a back office, or a third-party integration with an open token. The PMS, POS and any guest-facing tools all hold sensitive data, and the protection job is mostly about doing the basics consistently.
â€Encrypt data at rest (AES-256 is table stakes) and in transit (TLS 1.2 or 1.3). If a laptop is stolen or a database is exfiltrated, encrypted data is mostly noise to the attacker. Card data should never sit on the property's systems in raw form. That is what tokenisation is for.
Firewalls keep external traffic to expected paths. More usefully, network segmentation keeps the guest Wi-Fi away from the back-office VLAN, the PMS away from the smart TV management console, and the IoT devices in their own bubble. Most large-scale hospitality breaches have a story of a flat network somewhere in the chain.
A password on the staff Wi-Fi is not security. WPA3 enterprise authentication, regular rotation of pre-shared keys for any guest-facing networks, VPN access for remote PMS work, and an honest map of what is on the network. How many properties can produce that map on demand? Far fewer than you would think.
Every device on the network is a potential entry point. EDR tooling on workstations, MDM on staff phones, and a clear policy on personal devices touching hotel systems. The latter is where small properties tend to slip: the GM uses their personal laptop to log into the PMS from home, and that laptop has not seen a security update since 2022.
â€
Three things, done consistently, beat any single piece of expensive software:
Get these three right and you cover most of the realistic threat surface in a hotel. The rest is paid attention rather than expensive software.
â€
â€
Compliance does not need to be done by hand. Two technology approaches do most of the heavy lifting in a hotel context:
Between automated compliance and behaviour-based threat detection, you cover most of the ground a hotel needs without putting a CISO on payroll.
â€
â€
The threat picture changes year over year. The 2026 view, with the caveats that come with any prediction:
The pattern is the usual one in cybersecurity: most of the value sits in the unglamorous things done consistently, with a thin layer of newer technology on top.
â€
Data security is not the part of the operation that gets photographed for the brand book. But it is the part that, if it fails, undoes a decade of work on reputation and guest trust. The job for an operator in 2026 is unromantic: pick vendors with credible security postures, sign DPAs that mean something, train the team, log everything, and rehearse the day a breach happens.
Data has weight in 2026: financial, legal and reputational. Properties that treat security as part of operations rather than an IT line item come out ahead. The boring discipline of doing the basics every quarter is, in the end, what protects guests and protects the business.
← Previous: Part 9: Integrations and APIs | Next: Part 11: The AI Operator Layer of the Hotel Tech Stack →
Robust encryption for data at rest and in transit, properly configured firewalls, network segmentation beyond a basic Wi-Fi setup, current endpoint security on every device, and a written incident response plan. Hotels that get those basics right cover most of the realistic threat surface; the rest is consistency.
Compliance protects hotels from fines and protects guest trust. The main regulations: GDPR for EU citizens' data, CCPA and CPRA for California residents, PCI DSS for payment card security, HIPAA where medical services are offered, and COPPA for under-13s. Each carries its own requirements and penalties for non-adherence.
AI and machine learning power behavioural threat detection, catching unusual logins or lateral movement that rule-based tools miss. Automated compliance platforms handle consent, retention and subject access requests at scale. Together they let mid-size groups run a credible security posture without a CISO on payroll.
Excessive data retention beyond reservation needs, and unsanctioned third-party data sharing (typically with marketing platforms or chatbot vendors without proper Data Processing Agreements). Hotels often retain guest data indefinitely 'in case of return' without a defined retention policy. That alone is a violation.
Use a tokenised payment layer (Mews Payments, Cloudbeds Payments, Adyen, Stripe) so card numbers never touch the property's systems. This drops PCI scope from SAQ-D (most stringent) to SAQ-A. Avoid taking card numbers over phone, email, or chat; always use tokenised collection links.
A signed Data Processing Agreement, EU data residency for EU operators, explicit data retention controls, opt-out mechanics for guests, audit logs per conversation, and confirmation that guest data is not used to train vendor models. Reject vendors who can't provide all six in writing.